The Challenge: Knowing Your Security Posture
Security and risk leaders lack security KPIs and data to effectively quantify and communicate organizational risk and manage the enterprise-wide cybersecurity posture and answer key questions in the face of threat evolutions and business driven IT and OT initiatives. Disparate tools and passive approaches to risk management lack concrete actionable data to drill down and know, for example:
How safe is your organization from ransomware right now and where is your weakest link?
How have business drivers, like working from home and cloud migration impacted organizational risk?
How susceptible are you to the tactics and techniques of APT groups targeting your industry?
The Solution
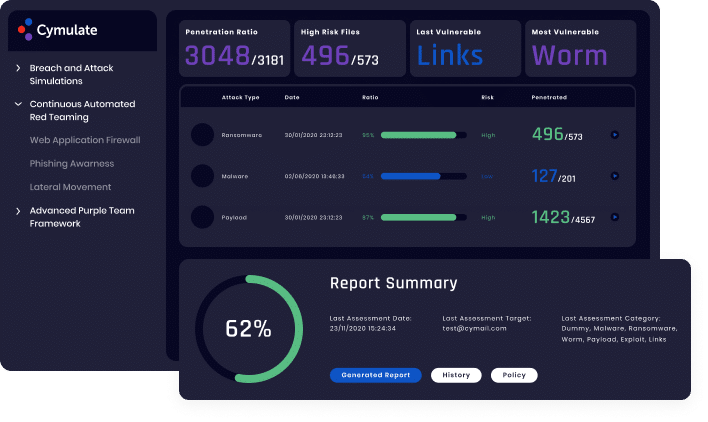
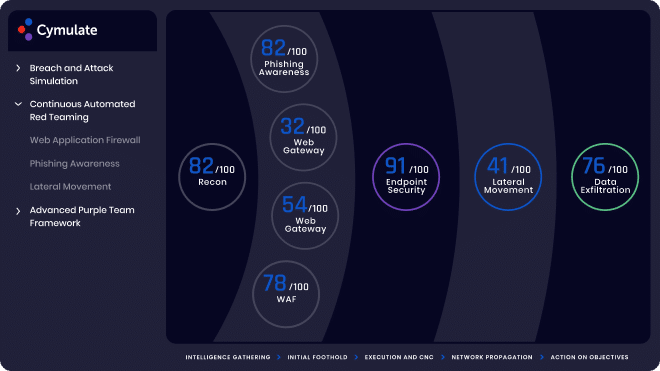
With the broadest coverage in the industry, Cymulate Continuous Security Validation helps to manage the cybersecurity posture across the entire organization. It takes a proactive approach by launching red team campaigns and purple team scenarios in a continuous and automated fashion.
Executive reports highlight high-risk security deficiencies and quantifies risk based on a consistent standards-based risk scoring methodology across all of the most important cybersecurity domains:
- Attack Surface Management
- xDR/SIEM/SOC Validation
- Security Control Validation
- Cloud Security Validation
- Vulnerability Management
- Employee Security Awareness
Automation of the security assurance process enables you to establish an enterprise-wide security baseline and continuously maximize your security posture, assure improved effectiveness, and prevent security drift.
Benefits

Automated Detailed Reports

Prevent Environmental Security Drift
End-to-End Baselining and Trending
Learn More
Simply Know
Control and assure the security posture
of your organization with the most
comprehensive Extended Security Posture Management platform.
More Solutions
Learn how Cymulate makes it easy to keep all angles of your company safe and secure.

Security Control Validation
Comprehensive SIEM/SOC and IR assessment with many scenarios permutations
SIEM Validation
Optimized SIEM Performance
with enhance detection and
reduced false positives
Mergers and Acquisitions
Comprehensive M&A security posture analysis of planned acquisitions
Operationalizing Threat Intelligence
Continuously updated emerging threats resilience evaluation

Cloud Security Validation
Continuous cloud security control validation and mitigation optimization

Attack Surface Management
Continuous Security Validation with 360°
exposure visibility, comprehensive
threat vector identification
and resilience scoring

Attack Based Vulnerability Prioritization
Data backed optimized mitigation prioritization

SOC and SOAR Validation
End-to-end threat detection and IR playbook optimization through comprehensive automated continuous security validation